Feed Reference
Reference details for analysts who want to know what they're looking at in MISP.
Common Wire Shape
Every event in every feed carries the same baseline:
| Field | Value |
|---|---|
Source organisation (Orgc) | ELLIO |
| Distribution | 0 - Your organisation only |
| TLP | tlp:amber+strict |
| Producer tag | misp-galaxy:producer="ELLIO" |
| Source tag | ellio:source="deception-network" |
| Decay tag | ellio:decay-model="ellio-deception-90d" |
| Classification tag | ellio:classification="..." - one of malicious, promiscuous, benign, unknown |
Threat level mirrors the worst kill-chain phase observed for the IP:
| Threat level | Kill-chain phases |
|---|---|
| High | Exploitation, Installation, C2, Actions on Objectives |
| Medium | Delivery |
| Low | Reconnaissance, Weaponisation |
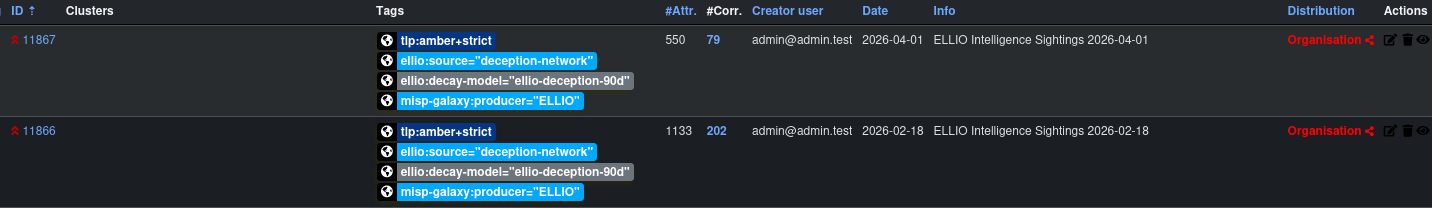
Daily Sightings - /daily/
A daily-sightings event is a single MISP object per calendar day carrying hundreds of thousands of ip-src attributes. MISP is built to handle many small events, not a few enormous ones, so this feed is only recommended for instances tuned for extreme performance. For ~99% of organisations the Per-IP rolling feed is the better choice and covers the majority of use cases - same source data, much lighter load on MISP.
One MISP event per calendar day in the rolling window. Event titles follow the pattern ELLIO Intelligence Sightings YYYY-MM-DD. Each active IP appears as a flat ip-src attribute on that day's event, carrying its day-specific tags (kill-chain phase, MITRE ATT&CK techniques, ellio:tag="...", classification).
- Sort order. Attributes are sorted by classification severity descending (malicious → promiscuous → benign → unknown), then by IP, so the most actionable indicators appear first in the UI.
- Analysis status. Today's event is
Ongoing; past days show asCompleted. - Aging. Every event carries the
ellio:decay-model="ellio-deception-90d"tag pointing at ELLIO's recommended 90-day curve. Configure a matching MISP decay model on your side and aging indicators score down - see the decay model page for parameters and theassociated_typescaveat.
When to use it: SIEM queries that ask "which IPs were active on YYYY-MM-DD", daily reporting, retrospective hunting against historical days.

Per-IP Rolling - /per-ip/
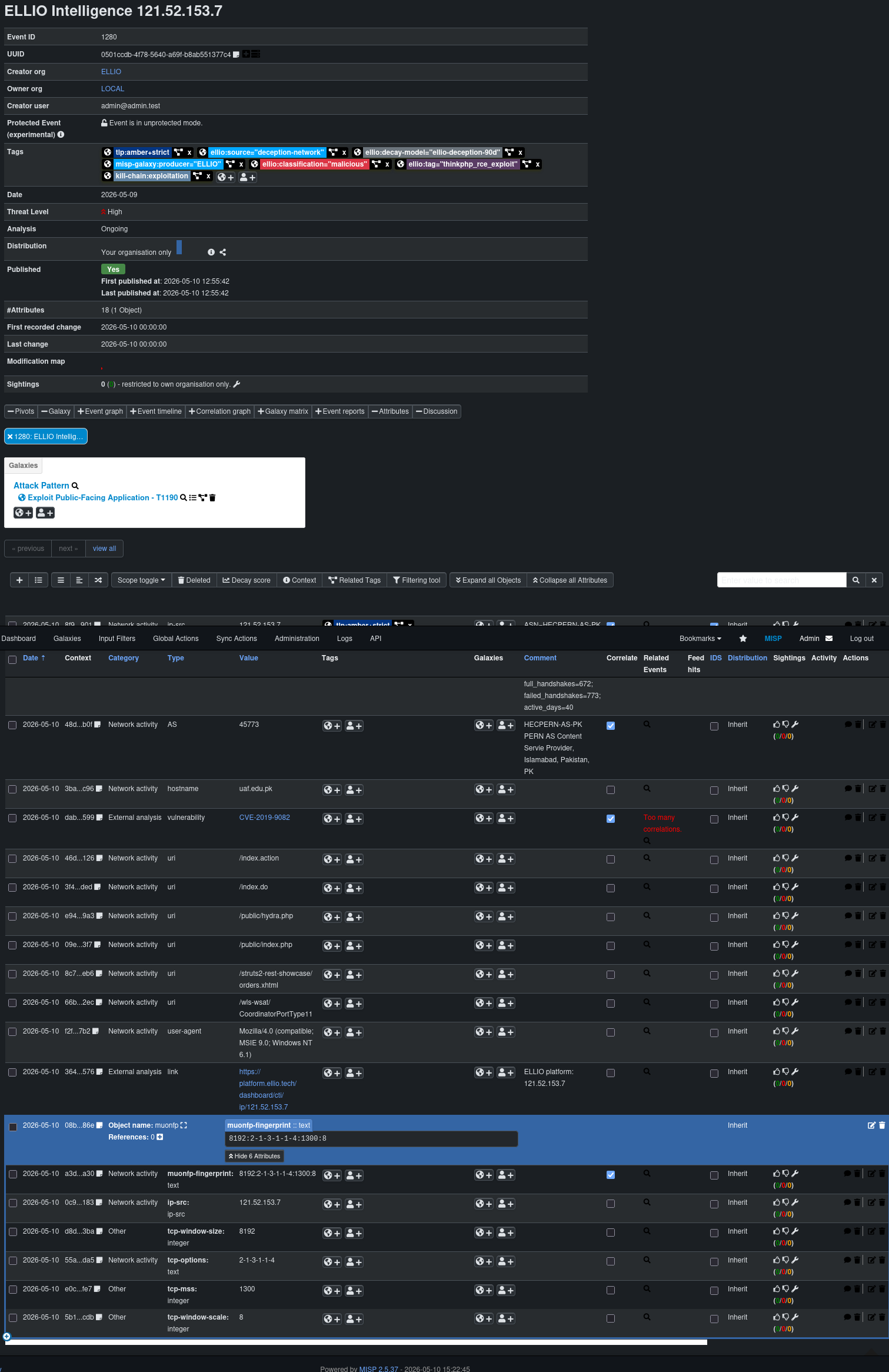
One event per source IP that has had at least one full TCP handshake in the rolling window. Spoofable IPs (no full handshake on any day in the window) are excluded. Event titles follow the pattern ELLIO Intelligence <IP>.

Each event carries a cross-day timeline of every observable signal attached to that IP. The time anchor varies by attribute type:
| Attribute | Time anchor |
|---|---|
ip-src | Event window (full 90 days observed for this IP) |
| AS, country-of-residence, hostname (rDNS) | Last observed day - these can change inside the window via BGP, geo, or PTR updates |
vulnerability (CVE) | Every day the IP was actively observed |
uri, user-agent, fingerprints (ja3, jarm, ja4 base) | Per-attribute first_seen / last_seen |
link (ELLIO platform backlink) | Event window |
ip-port Object (port + status) | Per-port first_seen / last_seen |
muonfp Object | Per-fingerprint first_seen / last_seen. Lets MISP correlate IPs that share fingerprint components. |
- MITRE ATT&CK ships as
misp-galaxy:mitre-attack-pattern="..."tags on the relevant attributes. MISP resolves those tags into Attack Pattern clusters in the UI when the misp-galaxy collection is installed (it is on every default MISP). - Aging. Every event carries the
ellio:decay-model="ellio-deception-90d"tag pointing at ELLIO's recommended 90-day curve. Configure a matching MISP decay model on your side and aging indicators score down - see the decay model page for parameters and theassociated_typescaveat. - Includes basic JA4 (
ja4) and the free non-JA4 fingerprints (ja3,jarm,muonfp). FoxIO-licensed JA4+ extensions ship in the JA4+ feed only.
When to use it: IOC correlation, pivoting from a single IP to its full behaviour, threat hunting, automated blocking decisions.
Per-IP Rolling with JA4+ - /per-ip-ja4plus/
Identical to the per-IP rolling feed plus the FoxIO-licensed JA4+ Object family - ja4s, ja4h, ja4l, ja4x, ja4ssh, ja4t, ja4ts, ja4tscan.
- Same event shape and time-anchor semantics as
/per-ip/. - Each JA4+ fingerprint ships as a typed MISP Object so MISP correlation works out of the box.
- Subscribing requires a FoxIO JA4+ licence. Without one, subscribe to
/per-ip/instead - you can swap later without losing data.
When to use it: high-fidelity client/server fingerprint correlation, attacker-tooling attribution, JA4-driven hunt rules.